I’ve spent a lot of time recently updating and refreshing all my sites and I recently migrated my vLaunchpad site to a new hosting provider, new WordPress version and to a new theme. I also took some time and went through the big backlog I had of adding new blogs to it. I’ve added at least 50 new blogs as I get ready for the upcoming top vBlog voting which will be kicking off in December. There are some cool changes in store for top vBlog this year so make sure your blog is listed on the vLaunchpad so it is included in the voting and you don’t miss out. I just updated the blog submission form so make sure you use that as it includes all the key info that I need to add your blog to it.
Oct 18 2014
Why the VMware vSphere TPS vulnerability is a big deal
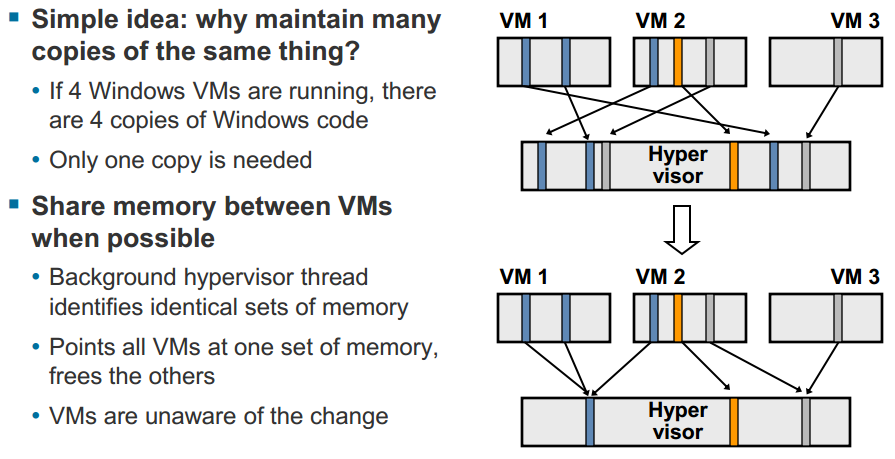
VMware recently acknowledged a vulnerability with their Transparent Page Sharing (TPS) feature that could potentially allow VM’s to access memory pages of other VMs running on a host. TPS is a host process that leverages the Virtual Machine Monitor (VMM) component of the VMkernel to scan physical host memory to identify redundant VM memory pages. The benefits of TPS are that it allows a host to reduce physical memory usage so you can squeeze more VMs onto a host as memory is often one of the most constrained resources on a host. TPS is basically the equivalent of storage de-duplication for RAM and works at the 4KB block level. You can read a full description on how it works in this classic VI3 memory white paper that refers to it as “Memory Sharing” or this more recent vSphere 5 white paper on memory management. Here’s a brief description of it and a slide on how it works:
[important]When multiple virtual machines are running, some of them may have identical sets of memory content. This presents opportunities for sharing memory across virtual machines (as well as sharing within a single virtual machine). For example, several virtual machines may be running the same guest operating system, have the same applications, or contain the same user data. With page sharing, the hypervisor can reclaim the redundant copies and keep only one copy, which is shared by multiple virtual machines in the host physical memory. As a result, the total virtual machine host memory consumption is reduced and a higher level of memory overcommitment is possible.[/important]
It’s important to note that the TPS feature is nothing new to vSphere having been first introduced with the VI3 release back in 2006, but apparently someone has now finally gotten around to try and successfully exploit it. Why is this a big deal? Because a virtualized architecture demands VM isolation, this is the most important security requirement for virtualization. Each VM guest running on a host must not be allowed in any way to access another VM guest. They must be kept in separate locked rooms with only the hypervisor possessing the keys to access all of them.
To illustrate this let’s use a real world scenario, imagine if you checked into a hotel, you expect privacy and isolation and to not have any other guests be able to come into your room. However your room has an adjoining shared door with another room but neither guest could get through it, only the hotel management can control the door. But somehow a guest has figured out a way to to open that door and get into your room and invade your privacy, that’s a pretty big deal wouldn’t you say.
VMware appears to be down-playing it as it obviously exposes a chink in their virtual armor, they have issued a KB article describing the vulnerability and giving guidance on how customers can disable TPS on their hosts. VMware doesn’t name the specific source that found the vulnerability in the KB article, they simply refer to it as “an academic paper”. The academic paper is entitled “Wait a minute! A fast, Cross-VM attack on AES” and was written by a group of individuals from Worcester Polytechnic Institute in 2014. It was funded by a National Science Foundation grant and it’s a pretty technical, head-spinning read with a lot of mathematical formulas. It’s worth taking a look at though as parts of it are more easily consumable and describe the attack scenarios and results. The overview of the paper is described as:
[important]In this work, we show a novel cache-based side-channel attack on AES that—by employing the Flush+Reload technique—enables, for the first time, a practical full key recovery attack across virtual machine boundaries in a realistic cloud-like server setting. The attack takes advantage of deduplication mechanism called the Transparent Page Sharing which is employed by VMware virtualization engine and is the focus of this work. The attack works well across cores, i.e. it works well in a high-end server with multiple cores scenario that is commonly found in cloud systems. The attack is, compared to [13], minimally invasive, significantly reducing requirements on the adversary: memory accesses are minimal and the accesses do not need to interrupt the victim process’ execution. This also means that the attack is hardly detectable by the victim. Last but not least, the attack is lightning fast: we show that, when running in a realistic scenario where an encryption server is attacked, the whole key is recovered in less than 10 seconds in non-virtualized setting (i.e. using a spy process) even across cores, and in less than a minute in virtualized setting across VM boundaries.[/important]
When I was going through the paper at the end of the paper in the references section one thing I noticed was that the authors of the paper had previously written a paper earlier in 2014 entitled “Fine grain Cross-VM Attacks on Xen and VMware are possible!“. So it appears based on that they worked to apply the theoretical research from that paper into a real-life attack which succeeded and prompted the 2nd paper to be written.
It’s important to note that this is not an easily exploitable vulnerability and the risk is super low so most environments should not really be impacted by it. VMware is being overly cautious though and will disable the feature by default in all upcoming releases of vSphere which includes:
- ESXi 5.5 Update release – Q1 2015
- ESXi 5.1 Update release – Q4 2014
- ESXi 5.0 Update release – Q1 2015
- The next major version of ESXi
In addition they will be issuing patches before that to address it sooner rather than later as follows:
- ESXi 5.5 Patch 3
- ESXi 5.1 patch planned for Q4, 2014
- ESXi 5.0 patch planned for Q4, 2014
All versions of vSphere back to VI3 are vulnerable to the exploit but VMware is only patching the 5.x versions of vSphere as the 4.x versions are no longer officially supported as of May 2014. Note these patches only disable TPS which is currently enable by default, they do nothing to fix the vulnerability, it will most likely take VMware some time to figure out how to make TPS work in a way that cannot be exploited. So if you disable TPS on your own you don’t really need the patch. VMware states in the KB article that “Administrators may revert to the previous behavior if they so wish” so it sounds like they are not too worried about it.
The benefits that TPS provides will vary in each environment depending on VM workloads so if you are really paranoid about security you will probably want to disable it. You can view the effectiveness of TPS in vCenter by looking at the “shared” and “sharedcommon” memory counters to see how much you benefit from it. You can disable TPS in your current environment by changing advanced settings on each host as described in the KB article, updating the setting is pretty simple but having it take effect is tedious work:
- Log in to ESX\ESXi or vCenter Server using the vSphere Client.
- If connected to vCenter Server, select the relevant ESX\ESXi host.
- In the Configuration tab, click Advanced Settings under the software section.
- In the Advanced Settings window, click Mem.
- Look for Mem.ShareScanGHz and set the value to 0.
- Click OK.
- Perform one of the following to make the TPS changes effective immediately:
- Migrate all the virtual machines to other host in cluster and back to original host.
- Shutdown and power-on the virtual machines.
While the impact and exposure may be minimal with this, the fact that someone has finally cracked those solid walls that have stood between VMs is a big deal. I’ve written about it previously in my post on Escaping the Cave, VMware officially describes this as “inter-process side channel leakage” and mentions this in the KB article:
[important]Side channel attacks that exploit information leakage from resources shared between processes running on a common processor is an area of research that has been explored for several years. Although largely theoretical, techniques are continuously improving as researchers build on each other’s work. Although this is not a problem unique to VMware technology, VMware does work with the research community to ensure that the issues are fully understood and to implement mitigation into our products when appropriate[/important]
Note they mention these types of vulnerabilities have been “explored” for years, meaning lots of people have been looking for a way to penetrate those walls as this is the holy grail type of hack of a virtual environment. Imagine if someone compromised a less critical VM through one of the many thousands of OS and application vulnerabilities that exist. At least the damage and exposure is contained within that one VM, but if some one could somehow use that compromised VM as a launchpad for attacking other VMs on a host that’s a real big deal. The fact that most of these types of vulnerabilities have been theoretical up until now really exposes VMware and their security foundation.
Overall vSphere is a very secure platform and has stood the test of time without any major issues which is a testament to how seriously they take security in vSphere. VMware will no doubt learn from this one and work to improve the security in vSphere to make it even better. However the circumstances of this one resulted from them trying to be more efficient with hypervisor resources by mixing VM data together. They will definitely need to be careful going forward as they continually look for new ways to optimize vSphere so they do it in a secure manner and do not risk exposure between VMs.
If you want to find out more about memory management in vSphere check out some of these links:
- Understanding Virtualization Memory Management Concepts (Great 2010 VMworld presentation from Kit Colbert)
- VMworld 2012: Session VSP1729 – Understanding Virtualized Memory Performance Management (Kit Colbert again)
- Understanding Memory Resource Management in VMware vSphere 5.0 (VMware tech paper)
- The Role of Memory in VMware ESX Server 3 (VMware tech paper)
- VMware vSphere 5 Memory Management and Diagram (VMware KB video)
Oct 12 2014
vSphere Metro Storage Cluster Links
EMC specific
Using VMware vSphere with EMC VPLEX (EMC Tech Paper)
Implementing vSphere Metro Storage Cluster (vMSC) using EMC VPLEX (2007545) (VMware KB)
HDS specific
Deploy VMware vSphere Metro Storage Cluster on Hitachi Virtual Storage Platform (HDS Tech Paper)
Implementing vSphere Metro Storage Cluster using Hitachi Storage Cluster for VMware vSphere (2073278) (VMware KB)
Deploying a vSphere Metro Storage Cluster (vMSC) using Hitachi NAS (HNAS) Platform with Synchronous Disaster Recovery (SyncDR) Cluster software in VMware vSphere (2085108) (VMware KB)
Implementing vSphere Metro Storage Cluster using Hitachi Storage Cluster for VMware vSphere (featuring Hitachi Virtual Storage Platform) (2039406) (VMware KB)
HP specific
Implementing vSphere Metro Storage Cluster using HP 3PAR Peer Persistence (HP Tech Paper)
Implementing VMware vSphere Metro Storage Cluster with HP LeftHand Multi-Site storage (HP Tech Paper)
VMware vSphere Metro Storage Cluster with HP 3PAR Peer Persistence – Part I (vCloudNine)
VMware vSphere Metro Storage Cluster with HP 3PAR Peer Persistence – Part II (vCloudNine)
Implementing vSphere Metro Storage Cluster using HP 3PAR StoreServ Peer Persistence (2055904) (VMware KB)
Implementing vSphere Metro Storage Cluster using HP LeftHand Multi-Site (2020097) (VMware KB)
IBM specific
Stretched Cluster on IBM SVC (Part 1) (CloudFix)
Stretched Cluster on IBM SVC (Part 2) (CloudFix)
Deploying Stretched vSphere clusters with Site Recovery Manager on SAN Volume Controller (Virtual Storage Speak)
Bridging datacenters with VMware vSphere and IBM SAN Volume Controller – Part 1 (Virtual Storage Speak)
Bridging datacenters with VMware vSphere and IBM SAN Volume Controller – Part 2 (Virtual Storage Speak)
Bridging datacenters with VMware vSphere and IBM SAN Volume Controller – Part 3 (Virtual Storage Speak)
Implementing vSphere Metro Storage Cluster using IBM System Storage SAN Volume Controller (2032346) (VMware KB)
VMware HA and vMotion with stretched IBM System Storage SAN Volume Controller Cluster (2000948) (VMware KB)
NetApp specific
A Continuous-Availability Solution for VMware vSphere and NetApp (NetApp Tech Paper)
MetroCluster Version 8.2.1 Best Practices for Implementation (NetApp Tech Paper)
VMware support with NetApp MetroCluster (1001783) (VMware KB)
General
How to automate vSphere Metro Storage Clusters, so VMs are running locally to storage (bmspeak)
VM Placement on a vSphere Metro Storage Cluster with VCAC (Grant Orchard)
vSphere Metro Stretched Cluster with vSphere 5.5 and PDL AutoRemove (Long White Virtual Clouds)
vSphere Metro Storage Cluster and GAD: Rise of HDS Virtual Storage Machine (Paul Meehan)
Metro Clustering on VMware (Plain Virtualization)
New VMware HCL category: vSphere Metro Stretched Cluster (Virtual Geek)
vSphere Metro Storage Cluster – steps for non-disruptive site failover (Virtual Stace)
VMware Metro Storage Cluster Explained – Part 1: The Challenge (Virtualization Software)
VMware Metro Storage Cluster Explained – Part 2: The Potential Solution (Virtualization Software)
vSphere Metro Storage Cluster solutions and PDL’s? (VMware vSphere Blog)
VMware vSphere Metro Storage Cluster Case Study (VMware Tech Paper)
Stretched Clusters and VMware vCenter Site Recovery Manager: Understanding the Options and Goals (VMware Tech Paper)
VMworld 2012: Session BCO1159 – Architecting and Operating a VMware vSphere Metro Storage Cluster (VMworld video)
Operating and architecting a vSphere Metro Storage Cluster based infrastructure (VMworld 2013 slides)
vSphere Metro Storage Cluster – Uniform vs Non-Uniform (Yellow Bricks)
vSphere Metro Storage Cluster storage latency requirements (Yellow Bricks)
Oct 11 2014
Vendor Specific Storage Links
Dell
Best Practices for Configuring DCB with VMware ESXi 5.1 and Dell EqualLogic Storage (Dell Tech Paper)
Best Practices when implementing VMware vSphere in a Dell EqualLogic PS Series SAN Environment (Dell Tech Paper)
Configuring an iDRAC vFlash partition as a datastore in VMware ESXi (Dell Tech Paper)
Configuring Dell PowerEdge VRTX shared storage for VMware vSphere Environment (Dell Tech Paper)
Configuring iDRAC vFlash as a VMware ESXi VMKernel Coredump Collector (Dell Tech Paper)
Configuring iSCSI Boot for EqualLogic SAN with Dell PowerEdge Servers and VMware ESXi 5.1 (Dell Tech Paper)
Configuring stateless boot using Dell customized VMware ESXi 5.0 (Dell Tech Paper)
EMC
Storage Protocol Choices & Storage Best Practices for vSphere (EMC Presentation)
Using EMC VNX Storage with VMware vSphere (EMC Tech Paper)
EMC Powerpath/VE for VMware vSphere Best Practices planning (EMC Tech Paper)
Using VMware vSphere Storage APIs For Array Integration With EMC Symmetrix (EMC Tech Paper)
VMware vStorage APIs For Array Integration With EMC VNX Series For NAS (EMC Tech Paper)
EMC VPLEX – vSphere 5.1 Stretched Cluster Best Practices (Virtualization Team)
VMware vSphere 5.5 vMotion on EMC VPLEX Metro (VMware Tech Paper)
Implementing EMC Symmetrix Virtual Provisioning with VMware vSphere (VMware Tech Paper)
HP
HP P4000 LeftHand SAN Solutions with VMware vSphere Best Practices (VMware Tech Paper)
VMware vSphere VAAI for HP LeftHand Storage performance benefits (HP Tech Paper)
HP StoreVirtual VSA Design and Configuration Guide (HP Tech Paper)
Best practices for deploying VMware vSphere 5 with VMware High Availability and Fault Tolerance on HP LeftHand Multi-Site SAN cluster (HP Tech Paper)
Implementing VMware vSphere Metro Storage Cluster with HP LeftHand Multi-Site storage (HP Tech Paper)
HP 3PAR Storage and VMware vSphere 5 best practices (HP Tech Paper)
HP XP7 Storage and VMware vSphere 5 Best Practices and Configuration Guide (HP Tech Paper)
VMware vSphere VAAI for HP 3PAR Storage performance benefits (VMware Tech Paper)
3PAR Utility Storage with VMware vSphere (VMware Tech Paper)
HP Enterprise Virtual Array Storage and VMware vSphere 4.0, 4.1 and 5.x configuration best practices (HP Tech Paper)
IBM
Deploying VMware vSphere 5.5 on IBM PureFlex System (IBM Tech Paper)
VMware vSphere best practices for IBM SAN Volume Controller and IBM Storwize family (IBM Tech Paper)
NetApp
NetApp TR-3808 – VMware vSphere and ESX 3.5 Multiprotocol Performance Comparison Using FC, iSCSI, and NFS (NetApp Tech Paper)
NetApp Storage Best Practices for VMware vSphere (NetApp Tech Paper)
vSphere 5 on NetApp MetroCluster Solution (NetApp Tech Paper)
FlexPod Datacenter with VMware vSphere 5.5 Update 1 and All-Flash FAS (NetApp Tech Paper)
VMware vSphere 5 on NetApp Clustered Data ONTAP (NetApp Tech Paper)
Pure Storage
Pure Storage and VMware Storage APIs for Array Integration—VAAI (Pure Storage)
Pure Storage and VMware vSphere Best Practices Guide (Pure Storage)
Using the Pure Storage Content Pack for VMware vCenter Log Insight (Pure Storage)
Oct 11 2014
Flash Storage Links
Understanding TLC NAND (Anandtech)
The SSD Anthology: Understanding SSDs and new drives from OCZ (Anandtech)
Threshold Voltage Distribution in MLC NAND Flash Memory: Characterization, Analysis, and Modeling (cmu.edu)
An Introduction to Flash Technology (Cormac Hogan)
Storage 101: Flash Storage Myths and Facts (Enterprise Storage Guide)
Solid State Drive Technology: Differences between SLC, MLC and TLC NAND (HP)
Understanding endurance and performance characteristics of HP solid state drives (HP)
What is the difference between MLC Flash and eMLC Flash, and is it required for Enterprise Flash? (Hu’s Blog)
All-Flash Array Performance Testing Framework (IDC)
Anatomy of SSDs (Linux Magazine)
NAND Flash Primer (Micron)
How Solid State Drives are Made (Micron)
NAND Flash 101: An Introduction to NAND Flash and How to Design It In to Your Next Product (Micron)
TLC, MLC, and SLC Devices (Micron)
NOR/NAND Flash Guide: Selecting a Flash Storage Solution (Micron)
Choosing the Right NAND (Micron)
Flash Memory Reliability – Read, Program, and Erase Latency Versus Endurance Cycling (NASA)
Introduction to Flash Memory (Pure Storage)
01: Why SSDs Are Awesome: An SSD Primer (Samsung)
02: Understanding SSD System Requirements: SATA Interface Basics (Samsung)
03: NAND Basics: Understanding the Technology Behind Your SSD (Samsung)
04: Understanding SSDs: A Peek Behind the Curtain (Samsung)
05: Maximize SSD Lifetime and Performance With Over-Provisioning (Samsung)
06: Protect Your Privacy: Security & Encryption Basics (Samsung)
07: Communicating With Your SSD: Understanding SMART Attributes (Samsung)
08: Benchmarking Utilities: What You Should Know (Samsung)
09: Why Integration Matters: What Samsung’s Vertical Integration Means to You (Samsung)
10: The Samsung Advantage: Why You Should Choose a Samsung SSD (Samsung)
11: Samsung Data Migration Software: The simplest way to get your new SSD up and running (Samsung)
12: Samsung Magician Software: OS Optimization Feature Overview (Samsung)
Floating Gate Basics (scu.ecu)
Increasing Flash SSD Reliability (Silicon Systems)
E‐MLC vs. MLC NAND Flash (Smart Storage Systems)
A detailed overview of flash management techniques (Smart Storage Systems)
Making the case for solid-state storage (Storage Magazine)
The truth about SSD performance benchmarks (Storage Magazine)
NAND vs. NOR Flash Memory Technology Overview (Toshiba)
MODELING THE PHYSICAL CHARACTERISTICS OF NAND FLASH MEMORY (Virginia.edu)
FAQ: Using SSDs with ESXi (VMware Front Experience)
Yaffs NAND flash failure mitigation (Yaffs.net)
Oct 11 2014
Storage Protocol Links
General
iSCSI Beats Fibre Channel at Interop 2011 (Video)
Storage Protocol Comparison – A vSphere Perspective (VMware vSphere Blog)
Storage Protocol Comparison (VMware Tech Paper)
The Debate-Why NFS vs Block Access for OS/Applications (vTexan)
iSCSI
A “Multivendor Post” on using iSCSI with VMware vSphere (Virtual Geek)
A “Multivendor Post” to help our mutual iSCSI customers using VMware (Virtual Geek)
Using iSCSI storage with vSphere (Storage Magazine)
Configuring VMware vSphere Software iSCSI with Dell Equallogic PS Series Storage (Equallogic)
How to Configure Openfiler iSCSI Storage for VMware ESX 4 (Xtravirt)
Putting your storage to the test – Part 1 iSCSI on Iomega IX4-200D (Gabe’s Virtual World)
How-to connect ESX4, vSphere to Openfiler iSCSI NAS (Vladan.fr)
EMC Virtual Infrastructure for Exchange 2007 using vSphere 4.0 and iSCSI (EMC)
How to setup basic software iSCSI for VMware vSphere (video)
iSCSI Design Considerations and Deployment Guide (VMware)
Converged Storage Infrastructure for VMware vSphere 4.1 (Broadcom)
Why can you not use NIC Teaming with iSCSI Binding? (VMware vSphere Blog)
How to configure ESXi to boot via Software iSCSI? (VMware vSphere Blog)
iSCSI Advanced Settings (VMware vSphere Blog)
Configuring Proper vSphere iSCSI Multipathing via Binding VMkernel Ports [Video] (Wahl Network)
NFS
NFS Best Practices – Part 1: Networking (Cormac Hogan)
NFS Best Practices – Part 2: Advanced Settings (Cormac Hogan)
NFS Best Practices – Part 3: Interoperability Considerations (Cormac Hogan)
NFS Best Practices – Part 4: Sizing Considerations (Cormac Hogan)
A “Multivendor Post” to help our mutual NFS customers using VMware (Virtual Geek)
Using NAS for virtual machines (Storage Magazine)
Putting your storage to the test Part 2 NFS on Iomega IX4-200D (Gabe’s Virtual World)
Best Practices for Running vSphere on NFS Storage (VMware)
NFS Block Sizes, Transfer Sizes & Locking (VMware vSphere Blog)
Load Balancing with NFS and Round-Robin DNS (VMware vSphere Blog)
Best Practices for Running vSphere on NFS Storage (VMware Tech Paper)
Republished: Dispelling Some VMware over NFS Myths (Scott Lowe)
Reasons For Using NFS With VMware Virtual Infrastructure (VM/ETC)
Fiber Channel over Ethernet (FCoE)
“FCoE vs. iSCSI – Making the Choice” from Interop Las Vegas 2011 (Stephen Foskett)
VMware ESX FCoE CNA Compatibility in Plain English (Stephen Foskett)
How FCoE and iSCSI Fit into Your Storage Strategy (NetApp Tech OnTap)
Fibre Channel over Ethernet in the Data Center: An Introduction (Cisco)
VMware’s Software FCoE (Fibre Channel over Ethernet) Adapter (VMware vSphere Blog)
Fiber Channel
SAN System Design and Deployment Guide (VMware)
Configuring and Troubleshooting N-Port ID Virtualization (VMware)
NPIV: N-Port ID Virtualization (VMware vSphere Blog)
Oct 11 2014
vSphere Storage API Links
VAAI (Array Integration)
Is VAAI beneficial with Virtual Storage Appliance (VSA) based solutions ? (CloudXC)
VAAI Comparison – Block versus NAS (Cormac Hogan)
VAAI UNMAP Performance Considerations (Cormac Hogan)
VAAI and VSA: The Benefits are Real (Enterprise Storage Guide)
VMware vSphere 4.1 vStorage APIs for Array Integration (VAAI) understanding (GeekSilver)
VAAI and Deployment – a Practical Example (NTPro.nl)
VMware VAAI pros and cons and the hidden fourth primitive (SearchVMware.com)
VMware VAAI Storage Array Support in Plain English (Stephen Foskett)
A Complete List of VMware VAAI Primitives (Stephen Foskett)
Exploring the performance benefits of VAAI (The Lower Case w)
vSphere 4.1 – What do the “vStorage APIs for Array Integration” mean to you? (Virtual Geek)
vSphere 4.1 and vStorage APIs for Array Integration (VAAI) (Virtual Storage Guy)
VMware vSphere VAAI Demo with NetApp (Virtual Storage Guy)
VAAI and the Unlimited VMs per Datastore Urban Myth (Virtualization Evangelist)
vStorage APIs for Array Integration (VAAI) (VMTN)
vStorage APIs for Array Integration FAQ (VMware KB)
VAAI Offloads and KAVG Latency (VMware vSphere Blog)
Low Level VAAI Behaviour (VMware vSphere Blog)
A brief history of VAAI & how VMware is contributing to T10 standards (VMware vSphere Blog)
VAAI Offload Failures & the role of the VMKernel Data Mover (VMware vSphere Blog)
VAAI Thin Provisioning Block Reclaim/UNMAP Issue (VMware vSphere Blog)
VAAI Thin Provisioning Block Reclaim/UNMAP In Action (VMware vSphere Blog)
VAAI Thin Provisioning Block Reclaim/UNMAP is back in 5.0U1 (VMware vSphere Blog)
VMware vSphere Storage APIs – Array Integration (VAAI) (VMware Tech Paper)
VAAI sweetness (Yellow Bricks)
Using ESXTOP to check VAAI primitive stats (Yellow Bricks)
vStorage APIs for Array Integration aka VAAI (Yellow Bricks)
vSphere 5, VAAI and the Death of the Storage Array (ZDNet)
VASA (Storage Awareness)
What is VMware VASA? Not Much (Yet) (Stephen Foskett)
VAMP (Multi-pathing)
Pluggable Storage Architecture (PSA) Deep-Dive – Part 1 (Cormac Hogan)
Pluggable Storage Architecture (PSA) Deep-Dive – Part 2 (Cormac Hogan)
VMware PSP and SATP in Plain English (Stephen Foskett)
Configure VMware ESX(i) Round Robin on EMC Storage (boche.net)
What’s that ALUA exactly? (Yellow Bricks)
Pluggable Storage Architecture, exploring the next version of ESX/vCenter (Yellow Bricks)
A couple important (ALUA and SRM) notes (Virtual Geek)
Understanding more about NMP RR and iooperationslimit=1 (Virtual Geek)
vSphere Introduces the Plug-n-Play SAN (Virtual Storage Guy)
VMware PSA, MPP, NMP, PSP, MRU, … And Tutti Quanti! (DeinosCloud)
Best practices for HP EVA, vSphere 4 and Round Robin multi-pathing (Ivobeerens.nl)
vSphere Round Robin MultiPathing (Phil the Virtualizer)
Multipathing policies in ESX 4.x (VMware KB)
Did you know that you can now prioritize I/O Paths in the event of a failover? (VMware vSphere Blog)
Configuration Settings for ALUA Devices (VMware vSphere Blog)
Path failure and related SATP/PSP behaviour (VMware vSphere Blog)
Oct 06 2014
So you have a virtualization blog, what are you doing to back it up?
Have you ever had that awful sick to your stomach, oh shit feeling when you just realized you lost a lot of important data whether it be photos, documents or other important stuff that can’t easily be replaced? It sucks doesn’t it, usually it takes just one instance like that to inspire us to start taking backups seriously. Unfortunately though it won’t bring back what you lost. Backups are one of those things that many people don’t think about especially when they store data on a location that is hosted on the internet.
There are a great many people that are blogging about virtualization these days and most of them are using WordPress as their platform of choice to do it. WordPress is an ideal platform for blogging but all that hard work you put into blogging could be wiped out if you don’t properly backup your WordPress site.
But doesn’t my hosting provider backup my site?
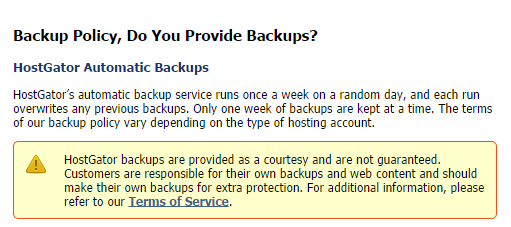
You should never trust that your hosting provider is backing up your website, many of them do not backup your content and if they do they probably do not guarantee them. Some hosting providers will offer a backup option as a paid add-on service. In addition they usually are not backing up your WordPress MySQL database which contains much of your valuable content. Take a look at this notice from my hosting provider, I think you’ll find the policy is similar with whatever provider you use, if you don’t know check with them.
How often should you backup your site?
Depending on how often you blog you should backup your WordPress instance at least once a month. If you are blogging several times a week you should probably do it daily or weekly. You should also do a backup before you upgrade WordPress to a newer version or update your plug-ins. Just like you do in the data center you should also plan on preserving older backups for as long as possible as often you may have something corrupted or malicious content that has been that way for a while that you need to go back a while to find a clean copy.
What should you backup?
With WordPress there are two main sets of data that you need to back up to ensure all your content is backed up and you can easily recover if needed, your WordPress files and your WordPress database. When you install WordPress on your website there are hundreds of files that get copied to specific directories that contain the complete WordPress web application. A new install of WordPress is only about 16MB in size with around 1,100 files but as you add content that will grow. Your WordPress database is typically hosted on a MySQL database that is installed and managed by your hosting provider. The WordPress database has many tables that store configuration and content for your WordPress website.
How do I back it up?
So now we know what needs to be backed up, how do we actually do it? There are several ways that you can backup WordPress:
- Manually by copying all your files to a PC using FTP and then doing a SQL export of your WordPress MySQL database and copying that to your local PC as well.
- Automatically by using some type of PHP script that can run scheduled on your hosting provider server using a scheduling tool like cron.
- Automatically using a WordPress plug-in designed to backup WordPress.
- Some hosting providers will do it if you pay for a add-on backup service.
Doing a manual backup
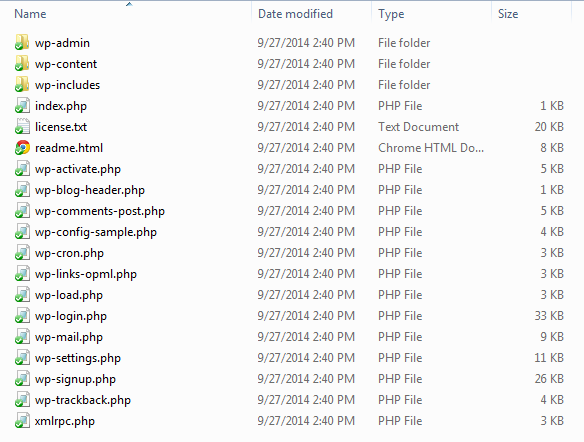
This method is OK for ad-hoc backups but it can be tedious to do on a frequent basis and it can easily slip your mind. I used this method for years, I did it nowhere near as often as I should of and I got lucky a few times were I almost lost a lot of data. To backup WordPress manually you will need to copy the all appropriate files and directories from the hosting provider web server to your local PC or even better to a cloud storage platform like Dropbox. Below are the files and directories that are come with a new install of WordPress.
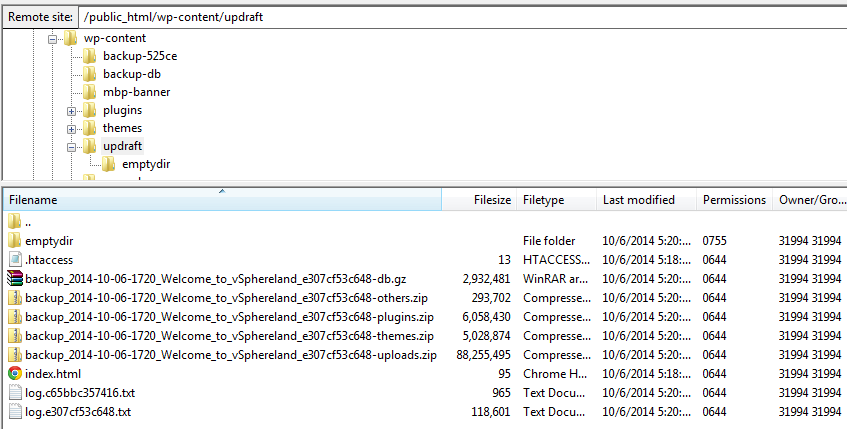
The easiest way to move the files is to use an FTP application to copy them from your old server to your local PC and then to your new server. It’s also a good idea to periodically do this to backup WordPress. If you need a FTP client, check out FileZilla which is a free open source application. You may need to setup a FTP username/password on your hosting site before you can connect to it. Create a new site in FileZilla and give it a name (i.e. mywebsite-old), use the IP address or DNS name of your website and then enter in your login credentials. Once you connect to your web server you’ll see the directory listing of the contents, what you see will usually vary by hosting providers, some providers partition you off so you don’t see much of the web server files.
You may not need all the files you see to backup WordPress but its best to copy everything to a sub-directory on your PC so you do have a full backup just in case. In the figure above you can see the 3 WordPress directories that you need to copy for sure along with all the files that start with “wp” in the root directory. I’ve manually copied things to my site in the past (i.e. images) which I copy also. Other files that are part of the hosting platform you typically don’t need to bring over but it doesn’t hurt to copy them any way. Once you’ve copied everything to your PC it’s time to move on to the next step, backing up your MySQL database.
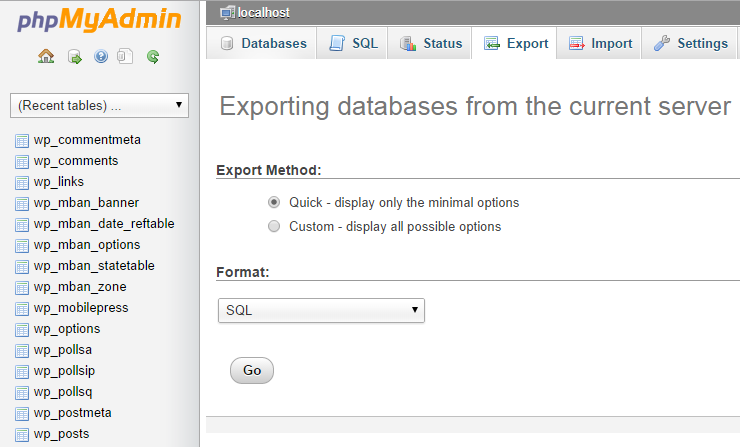
Your WordPress database is typically hosted on a MySQL database that is installed and managed by your hosting provider. The WordPress database has many tables that store configuration and content for your WordPress website. You can find a complete description of the database tables here. Log into your hosting provider control panel for your website and you should see a link for database management via phpMyAdmin which is a free software tool that is written in PHP that is used to administer MySQL over the Web. Once you launch phpMyAdmin you should be prompted for a username and password to connect to your database. You probably won’t know it or remember it but you can easily look it up by opening the wpconfig.php file that you copied to your PC as part of the backup in a text editor like Notepad and looking for the MySQL section which will contain your MySQL username/password.
Note some hosting providers may require you to whitelist your IP address to do remote MySQL administration, if they do there should be a section in your hosting control panel to put in your IP address. Once you are logged into phpMyAdmin you want to Export your database, click the Export link. You may be prompted for a quick export where you don’t need to enter a lot of options which will work just fine, if you do get a selection screen you typically can just use the defaults and then just hit Go and it will ask you for a location for the file on your PC and then begin the Export. It shouldn’t take more than a few minutes. Here’s how the Export screen looks with my hosting provider:
Once you have completed this it will create a .SQL file on your local PC that you should save with the other WordPress files that you copied. You now have everything you need to restore WordPress if needed by copying all the files you backed up back to the server and Importing the .SQL file back into WordPress, see my other post on moving to a new hosting provider for more info on how to do that.
Also note some hosting providers like GoDaddy provide a link in their control panel to kick off a database backup so you don’t have to go into PHPMyAdmin. They dump the resulting .SQL file in a db backup directory on your website, just make sure you copy the file from there to your local PC.
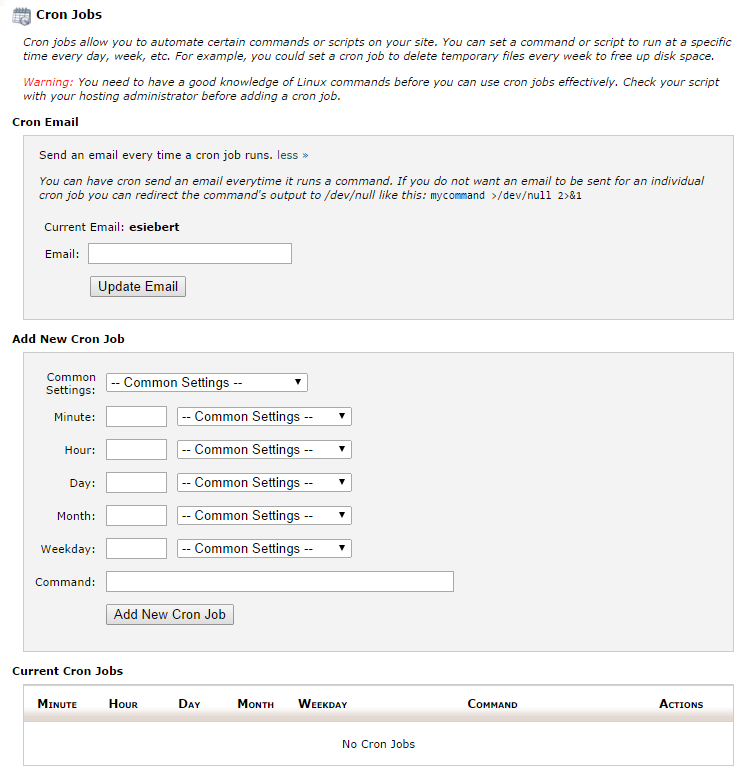
Doing an automatic backup with a PHP script and cron
I’m not going to go into much detail on this method, it can be a bit technical to setup. There are some WordPress plug-ins available that will make this easier to setup. Your hosting provider control panel should have a section to setup and manage cron jobs like below:
You then need to configure the scheduling and action for the cron job for the cron job to perform like below:
Again look for some WordPress plug-ins that support cron or a PHP script that is written to backup WordPress MySQL databases. If you are feeling adventurous you could also write your own PHP script. Here’s one I found by searching the internet. Some scripts may only backup the database so make sure you know what the script is doing and where it is storing your backups.
Doing an automatic backup with WordPress plug-in
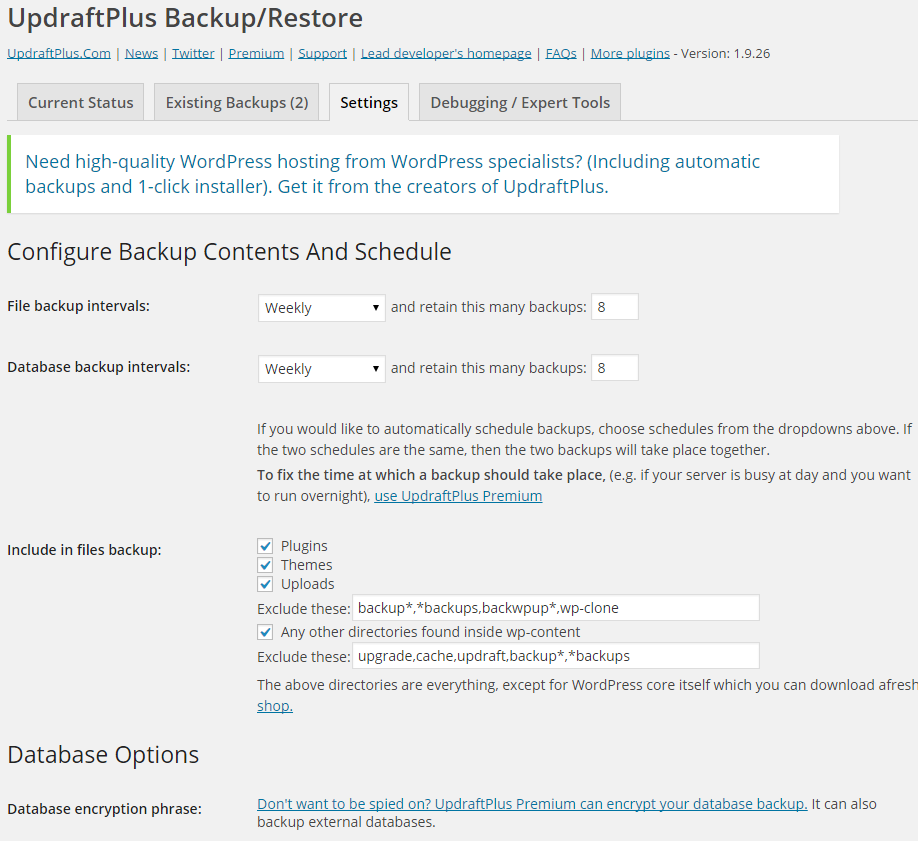
This is probably the easiest and most convenient way to backup your WordPress site. There are many plug-ins available that will automate the backup of both your WordPress files and MySQL database so you don’t have to do anything but install the plug-in and configure it. You can search through the WordPress plug-in directory and you’ll see many of them. The one I ended up using which had 4.8 out of 5 stars and is free but has some paid add-on’s is UpDraftPlus Backup & Restoration. You can go to their add-on page which contains a big list of add-on’s and pricing for each that expand the flexibility, functionality and backup targets supported. Another popular WordPress backup plug-in is BackWPup.
You can backup your site just fine with the free version but it only puts the backup files on your hosting web server. If you want to use other backup destinations like Dropbox, Amazon E3, Rackspace, Google Drive and more it will cost you about $10 for each. If you do backup to your website only just remember to copy those files off periodically to somewhere safe.
Install UpDraftPlus like you would any other WordPress plug-in, once activated go into Settings, UpDraftPlus Backups in WordPress to setup your backup jobs and you will be at the main screen:
Here you can see your backup status and quick actions for backing up and restoring. It’s best to click on the Settings tab first to configure backup schedules and retention. Since most hosting providers now provide unlimited space don’t be afraid to retain a lot of backups.
You can also specify what files to backup, database encryption if you are really paranoid, reporting, remote storage options and other advanced settings. Note by default with the free version it will not backup your core WordPress files (i.e. wp-admin) but unless you customize yours you won’t have to worry about those as you can easily download those again if needed. All the files specific to your WordPress site are in the Themes and Plugins directories.
Once the backup runs you can look at the log files to see everything that occurred during the backup, it’s not something you’ll need to do regularly but I looked as I was curious. If you are using the free version which puts the backups into your WordPress directory you’ll see a new sub-directory under wp-content called updraft that contains your backup files all zipped up, make sure you backup these backup files somewhere else!
What about Backup as a Service?
If you prefer not to deal with your backups at all you can outsource them to a company that provides backup services for WordPress. Note both of these companies below backup both your WordPress files and database.
One such company that does this is blogVault. Their Basic plan starts at $9/month for backing up a single site and retain 30 days of backups. If you have more than one site you they have a Plus plan for $19/month that will backup 3 sites. It works by installing their WordPress plug-in on your site and then their server automatically contacts the plugin everyday to backup new changes to your site.
Another company that provides WordPress backup services is Backup Buddy. Their Blogger plan rate is $80/year for backing up 2 sites with 1GB of backup space available. Presumably with that much space available you could store more than 60 days of backups with them. They also have a Freelancer plan available for $100/year for up to 10 sites with 1GB of backup space. Again it works by installing their WordPress plug-in on your site and then configuring it, they have a video that demonstrates this process.
Summary
And that’s all there is to it, pick the service/method/plug-in that works best for you. For me I’ve setup UpDraftPlus and will also periodically do manual backups as well. Regardless of how you do it the important thing is that you are backing up your WordPress site which contains all your hard work that you do not want to ever take the chance of losing.