The vCMA is considered a “Fling” which means it is an experimental app that is not officially supported and more of technology preview. The vCMA has been out for over a year and can be used for mobile devices to provide web-based basic administration of vSphere. I first downloaded the vCenter Mobile Access (vCMA) virtual appliance from VMware’s website a few weeks ago in preparation for the iPad vSphere Client application that is due to be released soon,VMware released an updated version of the vCMA in February that added support for the vSphere Client iPad application.
After installing the vCMA I found a really big security hole with it, by default all client connections to it are made over http and there is no support for enabling https. This means all the traffic between your mobile devices and the vCMA is in plain text, including your login credentials to hosts and vCenter Server. I ran a sniffer on my PC to prove this and saw my login information clear as day. I looked around in the vCMA forum and found a post from someone at VMware that gave general instructions for enabling https. It was not an easy process at all and involved creating your own certificates and modifying files inside the vCMA operating system. Most users would not be able to do this on their own.
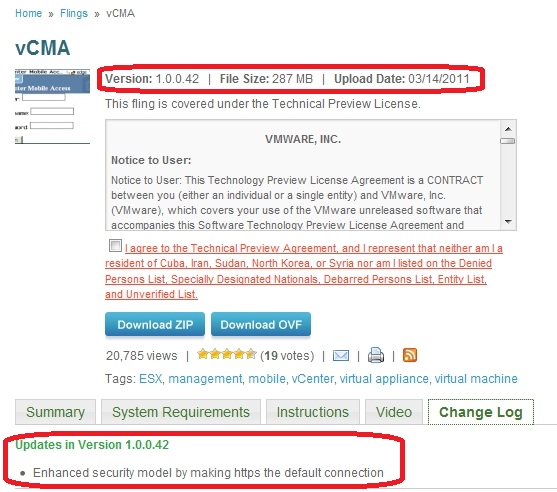
I brought this to VMware’s attention, I couldn’t believe that they did not have https support for the vCMA, this should of been the highest priority above everything else. Well VMware agreed and they quickly responded and turned around a new version of the vCMA inside of 2 weeks time. The new version now has https enabled by default using a certificate that VMware installed on the appliance so all network traffic is safe and sound.
So if you already have the vCMA installed make sure you download and install the new version of it as you run a great risk using it un-secured.