vSphere 6.7 is here and with support for vSphere 5.5 ending soon (Sept.) many people will be considering upgrading to it. Before you rush in though there is some important information about this release that you should be aware of. First let’s talk upgrade paths, you can’t just upgrade from any prior vSphere version to this release, only direct upgrades from certain versions are supported, see the below migration chart.
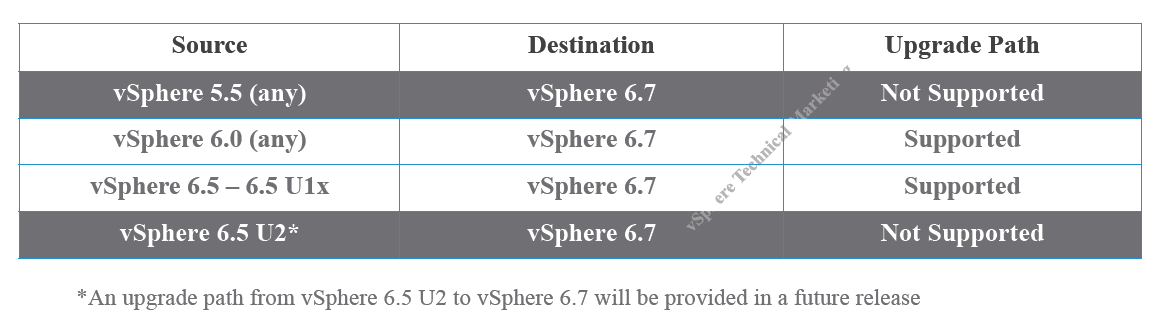 So duly note that upgrades to vSphere 6.7 are only possible from vSphere 6.0 or vSphere 6.5. If you are currently running vSphere 5.5, you must first upgrade to either vSphere 6.0 or vSphere 6.5 before upgrading to vSphere 6.7.
So duly note that upgrades to vSphere 6.7 are only possible from vSphere 6.0 or vSphere 6.5. If you are currently running vSphere 5.5, you must first upgrade to either vSphere 6.0 or vSphere 6.5 before upgrading to vSphere 6.7.
Next know that vSphere 6.7 is the absolute final release for the Windows version of vCenter Server and the Flex vSphere web client. VMware claims that the new HTML5 web client is much better in this release but it is not yet fully functional, VMware claims is it about 95% there so there may be things you still can’t do in it yet. The 6.7 release notes state this:
[important]In vSphere 6.7, the vSphere Client (HTML5) has many new features and is close to being a fully functional client with all the capabilities of vSphere Web Client (Flex). The majority of the features required to manage vCenter Server operations are available in this version, including vSAN and initial support for vSphere Update Manager (VUM). For an up-to-date list of unsupported functionality, see Functionality Updates for the vSphere Client Guide. vSphere 6.7 continues to offer the vSphere Web Client, which you can use for all advanced vCenter Server operations missing in the vSphere Client. However, VMware plans to deprecate the vSphere Web Client in future releases. For more information, see Goodbye, vSphere Web Client.[/important]
If you leverage vSphere APIs and use plug-ins also know this:
[important]The vSphere 6.7 release is the final release for two sets of vSphere client APIs: the vSphere Web Client APIs (Flex) and the current set of vSphere Client APIs (HTML5), also known as the Bridge APIs. A new set of vSphere Client APIs are included as part of the vSphere 6.7 release. These new APIs are designed to scale and support the use cases and improved security, design, and extensibility of the vSphere Client. VMware is deprecating webplatform.js, which will be replaced with an improved way to push updates into partner plugin solutions without any lifecycle dependencies on vSphere Client SDK updates. Note: If you have an existing plugin solution to the vSphere Client, you must upgrade the Virgo server. Existing vSphere Client plugins will not be compatible with the vSphere 6.7 release unless you make this upgrade. See Upgrading Your Plug-in To Maintain Compatibility with vSphere Client SDK 6.7 for information on upgrading the Virgo server.[/important]
TLS is a transport protocol that allows components to securely communicate with each other. In vSphere 6.7 VMware made a move to force better security so TLS 1.2 is now the default. Prior to 6.7 TLS 1.0 was the default for many VMware products, with TLS 1.2 now the default across the board this could potentially break some integration with 3rd party tools unless the vendor has support for TLS 1.2 as TLS 1.0/1.1 are now disabled. This KB article has a good VMware product matrix with TLS support default options prior to 6.7. This doesn’t mean support for TLS 1.0/1.1 is gone it’s just not enabled by default, it can be re-enabled if needed on a product by product basis (not recommended though). Here’s what the 6.7 release notes say about this:
[important]In vSphere 6.7, only TLS 1.2 is enabled by default. TLS 1.0 and TLS 1.1 are disabled by default. If you upgrade vCenter Server or Platform Services Controller to vSphere 6.7, and that vCenter Server instance or Platform Services Controller instance connects to ESXi hosts, other vCenter Server instances, or other services, you might encounter communication problems. To resolve this issue, you can use the TLS Configurator utility to enable older versions of the protocol temporarily on vSphere 6.7 systems. You can then disable the older, less secure versions after all connections use TLS 1.2. For information, see Managing TLS Protocol Configuration with the TLS Configurator Utility in the vSphere 6.5 Documentation Set. In the vSphere 6.7 release, vCenter Server does not support the TLS 1.2 connection for Oracle databases.[/important]
vSphere 6.7 introduces virtual hardware version 14 (HW compatibility level) which is necessary to take advantage of some of the new features in vSphere 6.7 like VBS, vTPM, vIOMMU, vPMEM and per-VM EVC. To use these features if you are upgrading from a previous version you must upgrade the hardware compatibility level to 14. However this could potentially cause disruption to the VM OS as upgrading is equivalent to replacing the motherboard of a computer. So it is recommended that you only upgrade to 14 if you really need to.
Some additional FYIs:
- The vSphere 6.7 release is the final release that supports replacing solution user certificates through the UI. Renewing these certificates with VMCA certificates through the UI will be supported in future releases.
- The vSphere 6.7 release is the final release that requires customers to specify SSO sites. This descriptor is not required for any vSphere functionality and will be removed. Future vSphere releases will not include SSO Sites as a customer configurable item.
On the good side upgrading a host now only requires a single re-boot so the process is less disruptive. See below for more detail on this:
 If you plan on upgrading to vSphere 6.7 note this important upgrade order for VMware products and components that must be followed to avoid issues, the hosts and VMs are at the very end of this order. The order is essentially this:
If you plan on upgrading to vSphere 6.7 note this important upgrade order for VMware products and components that must be followed to avoid issues, the hosts and VMs are at the very end of this order. The order is essentially this:
- vRA->vRO->vRB->vROPS->vRLI->VADP backup solutions->NSX->External PSC->vCenter Server->VUM->VR->SRM->UMDS->ESXi->vSAN->Virtual Hardware->VMware Tools
So make sure you do your homework before you upgrade to vSphere 6.7, read through the documentation, make sure all your 3rd party tools support it, check the VMware Hardware Compatibility Guide and be prepared. There are a lot of good things in this release so make sure you are ready before you dive into it.



